Registration Code Email Password Recovery Master
Advanced Office Password Recovery Full Version solutions allow gaining access to password-protected, locked and encrypted information created in a variety of applications. Our unique technologies and deep knowledge in information security implemented in our products allow investigators recovering the most complex passwords faster or even instantly. Registration code facebook password recovery master. I am unable to recover my facebook account when i try the three friends recovery method i get 'your account is temporarily unavailable. Regain ac; When resetting your facebook password by choosing 3 friends to make sure you are the account holder all of my 3 friends that i have chosen had got an.
Configure Guest Access. Cisco ISE Guest Services Cisco Identity Services Engine (ISE) guest services enable you to provide secure network access to guests such as visitors, contractors, consultants, and customers. You can support guests with base Cisco ISE licenses, and you can choose from several deployment options depending on your company’s infrastructure and feature requirements. Cisco ISE provides web-based and mobile portals to provide on-boarding for guests (and even employees) to your company’s network and internal resources and services. From the Admin portal, you can create and edit guest and sponsor portals, configure guest access privileges by defining their guest type, and assign sponsor privileges for creating and managing guest accounts. Guest Services are configured on the following pages:. End-User Guest and Sponsor Portals in Distributed Environment Cisco ISE end-user web portals depend on the Administration, Policy Services, and Monitoring personas to provide configuration, session support, and reporting functionality.
Administration Node Any configuration changes you make to users or devices on the end-user portals are written to the Administration node. Policy Services Node You must run the end-user portals on a Policy Services Node, which handles all session traffic, including: network access, client provisioning, guest services, posture, and profiling. If the Policy Service Node is part of a node group, and the node fails, the other nodes detect the failure and reset any pending sessions. Monitoring Node The Monitoring node collects, aggregates, and reports data about the end user and device activity on the My Devices, Sponsor, and Guest portals. If the primary Monitoring node fails, the secondary Monitoring node automatically becomes the primary Monitoring node. Guest and Sponsor Accounts Guest services support various types of users—guests, sponsors, and employees. On the Admin portal, you define the access privileges and feature support for sponsors.
Sponsors then access the Sponsor portal to create and manage guest accounts. Once their guest accounts are created, guests can use the Sponsored-Guest portal to log in and gain access to the network. Guests can also create their own accounts by registering themselves on the Self-Registered Guest portal. Based on the portal configuration, these self-registering guests may need sponsor approval before they receive their login credentials.
Guests can also choose to access the network using the Hotspot Guest portal, which does not require the creation of guest accounts and login credentials, such as username and password. Employees who are included in identity stores (such as Active Directory, LDAP, Internal Users) can also gain access through the credentialed Guest portals (Sponsored-Guest and Self-Registered Guest portals), if configured. Guest Accounts Guests typically represent authorized visitors, contractors, customers, or other users who require temporary access to your network. You can also use guest accounts for employees if you prefer to use one of the guest deployment scenarios to allow employees to access the network. You can access the Sponsor portal to view guest accounts created by a sponsor and by self-registering guests.
Sponsor Accounts Use the Sponsor portal to create temporary accounts for authorized visitors to securely access your corporate network or the Internet. After creating the guest accounts, you also can use the Sponsor portal to manage these accounts and provide account details to the guests. Guest Accounts Guests typically represent authorized visitors, contractors, customers, or other temporary users who require access to your network.
However, you can also use guest accounts for employees if you prefer to use one of the guest deployment scenarios to allow employees to access the network. You can access the Sponsor portal to view guest accounts created by a sponsor and by self-registering guests. Guest Types and User Identity Groups Guest accounts must be associated with a guest type. Guest types allow a sponsor to assign different levels of access and different network connection times to a guest account. These guest types are associated with particular network access policies. Cisco ISE includes these default guest types:. Contractor—Users who need access to the network for an extended amount of time, up to a year.
Daily—Guests who need access to the resources on the network for just 1 to 5 days. Weekly—Users who need access to the network for a couple of weeks. When creating guest accounts, certain sponsor groups can be restricted to using specific guest types. Members of such a group can create guests with only the features specified for their guest type. For instance, the sponsor group, ALLACCOUNTS, can be set up to use only the Contractor guest type, and the sponsor groups, OWNACCOUNTS and GROUPACCOUNTS, can be set up to use Daily and Weekly guest types. Also, since self-registering guests using the Self-Registered Guest portal typically need access for just a day, you can assign them the Daily guest type.
The guest type defines the user identity group for a guest. User identity groups are configured in Administration Identity Management Groups User Identity Groups. You can delete a user identity group for a guest only by deleting the specific guest type.
For more information, see:. Create or Edit Guest Types You can edit the default Guest Types and their default access privileges and settings, or you can create new Guest Types. Changes you make will be applied to existing Guest accounts that were created using this Guest Type. Guest users who are logged on will not see these changes until they log off and back on. You can also duplicate a Guest Type to create additional Guest Types with the same access privileges.
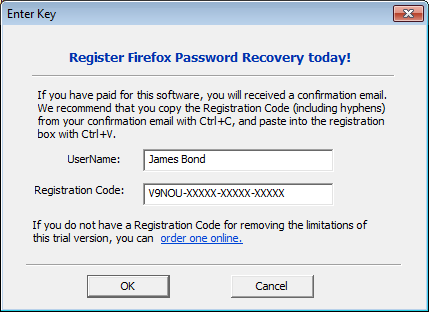
Email Password Recovery
Each Guest Type has a name, description, and a list of sponsor groups that can create guest accounts with this guest type. You can designate some guest types as follows: use just for self-registering guests, or do not use to create Guest accounts (by any sponsor group).
Fill in the following fields, which are described below. Guest type name—Provide a name (from 1 to 256 characters) that distinguishes this Guest Type from the default Guest Types and others that you create. Description—Provide additional information (maximum of 2000 characters) about the recommended use of this Guest Type, for example, Use for self-registering Guests, do not use for Guest account creation, and so forth. Language File—This field allows you to export and import the language file, which contains content for email subject, email message, and SMS messages in all supported languages. These languages and content are used in notifications that an account expired, which are sent to guests who are assigned to this guest type.
If you are creating a new guest type, this feature is disabled until you save the guest type. For more information about editing the lanaguage file, see. Collect Additional Data—Select custom fields to collect additional information from Guests. Custom fields are managed on Work Centers Guest Access Settings Custom Fields. Maximum Access Time. Account duration starts—If you select From first login, the account start time starts when the guest user first logs in to the guest portal, and the end time equals the specified duration time.
If the guest user never logs in, the account remains in the Awaiting first login state until the Guest Account Purge Policy removes the account. Self-registered user's account starts when they create and log on to their account. If you select From sponsor-specified date, enter the maximum number of days, hours, or minutes that Guests of this Guest Type can access and stay connected to the network. If you change this setting, your changes will not apply to existing Guest accounts created using this Guest Type. Value ranges from 1 to 999. Maximum account duration—Enter the number of days, hours, or minutes that guests assigned to this guest type can log on.
Note The account purge policy checks for expired guest accounts, and sends expiration notification. This job runs every 20 minutes, so if you set the account duration to less than 20 mins, it is possible that expiration notices may not be sent out before the account is purged. You can specify the duration time and the week days on which access is provided to the guests of this Guest Type by using the Allow access only on these days and times option. The days of the week that you select limits the dates that are selectable in the Sponsor's calendar. Maximum account duration is enforced in the sponsor portal when picking duration and dates.
The settings you make here for access time affect the time settings that are available on the sponsor portal when creating a guest account. For more information, see.
Logon Options. Maximum simultaneous logins—Enter the maximum number of user sessions that this Guest Type can have running concurrently. When guest exceeds limit—When you select Maximum simultaneous logins, you must also select the action to take when a user connects after that limit is reached. Disconnect the oldest connection. Disconnect the newest connection—Optionally select Redirect user to a portal page showing an error message: An error message is displayed for a configurable amount of time, then the session is disconnected, and the user is redirected to the Guest portal. The error page's content is configured on the Portal Page Customization dialog, on the Messages Error Messages.
Maximum devices guests can register—Enter the maximum number of devices that can be registered to each Guest. You can set the limit to a number lower than what is already registered for the Guests of this Guest Type. This only affects newly created Guest accounts.
Endpoint identity group for guest device registration—Choose an endpoint identity group to track guest devices. Cisco ISE provides the GuestEndpoints endpoint identity group to use as a default. You can also create more endpoint identity groups if you choose to not use the default. Allow guest to bypass the Guest portal—Allows users to bypass the credentialed Guest captive portal (web authentication page) and access the network by providing credentials to wired and wireless (dot1x) supplicants or VPN clients. Guest accounts go to Active state bypassing the Awaiting Initial Login state and the AUP page, even if it is required.
If you do not enable this setting, users must first log in through the credentialed Guest captive portal before they are able to access other parts of the network. Account Expiration Notification. Send account expiration notification days before account expires—Send a notification to Guests before their account expires and specify how many days, hours, or minutes before the expiration. View messages in—Specify the language to use when displaying email or SMS notifications as you set them up. Email—Send account expiration notices by email.
Use customization from—Apply the same customizations that you configured for the selected portal to this Guest Type's account expiration emails. Copy text from—Reuse email text that you created for another Guest Type's account expiration email. Send test email to me at. SMS—Send account expiration notices by SMS. The settings that follow for SMS are the same as for email notifications, except that you choose an SMS gateway for Send test SMS to me.
Sponsor Groups—Specify the sponsor groups who can create a guest account using this guest type. Delete the sponsor groups that you do not want to have access to this guest type. What to Do Next. Create or modify sponsor groups to use this guest type.
For more information, see. If appropriate, assign this guest type to self-registering guests in the Self-Registered Guest portal.
For more information, see. Disable Guest Types You cannot delete the last remaining guest type or guest types that are being used by guest accounts. If you want to delete a guest type that is in use, first ensure that it is no longer available for use. Disabling a guest type does not affect guest accounts that were created with that guest type. Step 1 Do one of the following or both, if appropriate:.
Choose Work Centers Guest Access Configure Guest Type and delete all sponsor groups using the specific guest type in Sponsor Groups. This action effectively prevents all sponsors from using it to create any new guest accounts. Choose Work Centers Guest Access Configure Guest Portals. Select the Self-Registered Guest portal that is using the specific guest type and change the assigned guest type for self-registering guests.
Step 2 Click Save and then Close. Changing Guest Account Attributes When a guest account is created, attributes are configured for that account by the Guest Type. If you make changes to a Guest Type, active Guest accounts will take on all the attributes of the updated Guest Type, including the default access times, dates, and duration, which can then be edited. In addition, the custom fields from the original Guest Type are copied to the updated Guest Type.
A Sponsor can also extend the account duration before the time period has expired. Configure Maximum Simultaneous Logins for Endpoint Users You can configure the maximum number of simultaneous logins that are allowed for Guest users.
When the user logs into the Guest portal, and is successfully authenticated, that user's number of existing logins is checked to see if the user has already reached the maximum number of logins. If so, then the Guest user is redirected to an error page. After a configurable period of time, so the user can read the error page, the session is terminated. If the user tries to access the internet again, that user is redirected to the Guest portal's login page. In an authorization policy, check for a value of true for the attribute Network Access.SessionLimitExceeded, and configure the action to take when the maximum number of sessions is reached. Before You Begin Make sure that the authorization profile that you are using in the authorization policy for this portal has Access Type set to AccessAccept. If Access Type is set to AccessReject, then maximum logins will not work.
Step 1 Choose Work Centers Guest Access Configure Guest Type, and under Login Options:. Enable Maximum simultaneous logins.
This is already enabled on the default Guest types. Select Disconnect the newest connection, select Redirect user to a portal page showing an error message, and choose the maximum number of simultaneous logins to allow. Step 2 Choose Policy Results, and create an authorization profile:. Under Common Tasks, Select Web Redirection, then:. In the first drop-down, select Centralized Web Auth. Enter the ACL you created as part of the prerequisite. For Value, select any Guest portal.
Select Reauthentication, then:. In Timer, enter the amount of time you would like the error page to appear before redirecting the user to the Guest portal login page. In Maintain Connectivity During Reauthentication, choose Default. Step 3 Browse to Policy Authorization, and create an authorization policy so that when the attribute NetworkAccess.SessionLimitExceeded is true, the user is redirected to the portal.
What to Do Next You can customize the text of the error page on the Portal Page Customization tab, in the tab Messages Error Messages by changing the text of the error message key uimaxloginsessionsexceedederror. Schedule When to Purge Expired Guest Accounts When an active or suspended guest account reaches the end of its account duration (as defined by the sponsor when creating the account), the account expires. When guest accounts expire, the affected guests cannot access the network. Sponsors can extend expired accounts before they are purged. However, after an account is purged, sponsors must create new accounts.
When expired guest accounts are purged, the associated endpoints and reporting and logging information are retained. Cisco ISE automatically purges expired guest accounts every 15 days, by default. The Date of next purge indicates when the next purge will occur. You can also:. Schedule a purge to occur every X days. The first purge will occur in X days at Time of Purge, then purges occur every X days. Schedule a purge on a given day of the week every X weeks.
The first purge occurs on the next Day of Week at Time of Purge, then purges occur every configured number of weeks on that day and time. For example, on Monday you set purges to occur on Thursday every 5 weeks.
The next purge will be the Thursday of this week, not the Thursday 5 weeks from now. Force a purge to happen immediately by clicking Purge Now. If the Cisco ISE server is down when the purge is scheduled to run, the purge is not executed. The purge process will run again at the next scheduled purge time, assuming the server is operational at that time. Step 1 Choose Work Centers Guest Access Settings Guest Account Purge Policy. Step 2 Choose one of these options:.
Click Purge Now to immediately purge the expired guest account records. Check Schedule purge of expired guest accounts to schedule a purge. Note After each purge is completed, the Date of next purge is reset to the next scheduled purge. Step 3 Specify after how many days of inactivity to purge user-specific portal records maintained in the Cisco ISE database for LDAP and Active Directory users. Step 4 Specify the number of days of inactivity to expire users in Expire portal-user information after. This setting prevents LDAP and Active Directory accounts that were never used from staying in the ISE database indefinitely. Step 5 Click Save.
If you do not want to save any updates you made to the settings, click Reset to revert to the last saved values. Add Custom Fields for Guest Account Creation When providing guest access, you may want to collect information from your guests beyond just their names, email addresses, and phone numbers. Cisco ISE provides custom fields that you can use to collect additional information about guests that is specific to your company’s needs.
You can associate the custom fields with guest types and with the Self-Registered Guest and Sponsor portals. Cisco ISE does not provide any default custom fields. Step 1 To add, edit, or delete custom fields for all Guest and Sponsor portals, choose Guest Access Settings Custom Fields. Step 2 Enter the Custom Field Name, pick a Data Type from the drop-down list, and enter Tip Text to help provide additional information about the custom field. For instance, if you enter Date of Birth, pick Date-MDY, and enter a tip for the date format as MM/DD/YYYY.
Step 3 Click Add. The custom field appears in the list in alphabetical order or in the context of the sorted order.
Step 4 Click Save. If you do not want to save any updates you made to the settings, click Reset to revert to the last saved values. Note If you delete a custom field, it will no longer be available for selection in the Custom Fields list for guest types and in the Self-Registered Guest and Sponsor portals settings. If the field is being used, Delete will be disabled.
What to Do Next You can include the desired custom fields:. When defining a guest type so that accounts created with that guest type will include this information. When configuring the Sponsor portal for sponsors to use when creating guest accounts. When requesting information from self-registering guests using a Self-Registered Guest portal. Specify Email Addresses and SMTP Servers for Email Notifications Cisco ISE allows you to send emails to sponsors and guests, notifying them of information and instructions. You can configure SMTP servers to deliver these email notifications.
You can also specify the email address from which the notifications will be sent to guests. Note Guest notifications require an UTF-8 compatible e-mail client.
Step 1 To specify email settings and configure SMTP servers for all Guest and Sponsor portals, choose Work Centers Guest Access Settings Guest Email Settings. Step 2 Enable email notifications to guests is checked by default.
If you disable this setting, guests will not receive email notifications regardless of any other settings you may have enabled while configuring Guest and Sponsor portals. Step 3 Enter the Default “From” email address that is designated for sending email notifications to guests. For example, donotreply@ yourcompany.com.
Step 4 Do one of the following:. Check Send notifications from sponsor's email address (if sponsored) if you want guests to receive notifications from the sponsor who created their accounts. Self-registering guests will receive notifications from the default email address. Check Always send notifications from the default email address if you want guests to receive notifications, regardless of whether they are sponsored and self-registering. Step 5 Click Save. If you do not want to save any updates you made to the settings, click Reset to revert to the last saved values. Assign Guest Locations and SSIDs A Guest Location defines a name for a time zone, and is used by ISE to enforce time-related settings of logged on Guests.
Guest Locations are assigned to Guest accounts by Sponsors creating a Guest account, and by self-registering Guests. The default Guest Location is San Jose.
If no other Guest Locations are added, all accounts are assigned this Guest Location. You can't delete the San Jose Guest Location unless you create one or more new Locations. Unless all your Guests will be in the same time-zone as San Jose, create at least one Guest Location with the required time-zone.

Note Guest access times are based on the Guest Location's time zone. A Guest user may not be able to login if the Guest Location's time zone doesn't match the system time zone. In this case, the Guest user may get an 'Authentication Failed' error. You might see the 'Guest active time period not yet started' error message in the debug report. As a workaround, you can adjust the Guest access start time to match the local time zone of the Guest user by using the Manage Accounts option. The SSIDs you add here are available to Sponsor Portals, so Sponsors can tell the Guest which SSID to connect to. You can't delete a Guest Location or a SSID if it is configured in a Sponsor portal or assigned to a Guest account.
Step 1 To add, edit or delete Guest Locations and SSIDs for Guest and Sponsor portals, choose Work Centers Guest Access Settings Guest Locations and SSIDs. Step 2 For Guest Locations:. For each time-zone that you need to support, enter a Location name and pick a Time zone from the drop-down list. Note In a Guest Location, the name of the place, the name of the time zone, and the GMT offset are static; you cannot change them. The GMT offset does not change with daylight savings time changes. The GMT offsets are the opposite of what is shown in the list. For example, Etc/GMT+3 is actually GMT-3.
Note For From First-login guest type, ensure that you configure a Guest Location (time zone) only if you intend to configure the access time restrictions in the Work Centers Guest Access Configure Guest Types page. Step 3 For Guest SSIDs:. Enter the SSID names of the networks that will be available for guests to use at the Guest Locations. Step 4 Click Save. To revert to the last saved values, click Reset.
What to Do Next If you added a new Guest Location or SSID, you can:. Provide the SSIDs for Sponsors to use when creating Guest accounts. Add the Guest Locations to Sponsor Groups, so Sponsors assigned to that group can use them when creating guest accounts. Assign the Guest Locations available to self-registering guests using a Self-Registered Guest portal.
For existing guest accounts, edit them manually to add SSIDs or Locations. Rules for Guest Password Policies Cisco ISE has the following built-in rules for guest passwords:. The Guest password policy applies to sponsor portals, self registered portals, accounts uploaded in a CSV file, passwords created using the ERS API, and user created passwords. Changes to the guest password policy do not affect existing accounts, until the guests passwords have expired and need to be changed.
Passwords are case sensitive. The special characters, /, and% cannot be used. Minimum length and minimum required characters apply to all passwords. Passwords cannot match usernames. New passwords cannot match current passwords.
Guests do not receive notifications prior to password expiration, unlike guest account expiration. When guest passwords expire, either sponsors can reset the password to a random password or guests can log in using their current login credentials and then change their password. Note The guest default username is four alpabetic and password is four numeric characters. Short, easy to remember usernames and passwords are adequate for short-term guests. You can change the username and password length in ISE, if you desire. Set the Guest Password Policy and Expiration You can define a password policy for all Guest portals.
A Guest password policy determines how the password is generated for all guest accounts. A password can be a mixture of alphabetic, numeric, or special characters. You can also set the number of days after which guest passwords will expire, requiring guests to reset their passwords. The Guest password policy applies to sponsor portals, self registered portals, accounts uploaded in a CSV file, passwords created using the ERS API, and user created passwords. Step 1 Choose Guest Access Settings Guest Password Policy. Step 2 Enter the Minimum password length (in characters) for the guest passwords.
Step 3 Specify the characters from each character set that can be used by guests to create passwords. Choose one of the following options under Allowed Characters and Minimums to specify the password policy for guests:.
Use all the characters from each character set. To prevent the use of certain characters, choose Custom from the drop-down menu, and delete these characters from the predefined and complete sets. Step 4 Enter the minimum number of characters to use from each set. The total number of required characters across the four character sets should not exceed the overall Minimum password length. Step 5 Choose one of the following options under Password Expiration:. Specify the frequency (in days) when guests have to change their passwords after they first log in.
If the guests do not reset their passwords before they expire, the next time they log in to the network using their original login credentials, they are prompted to change their passwords. Set the passwords to never expire. Step 6 Click Save. If you do not want to save any updates you made to the settings, click Reset to revert to the last saved values.
What to Do Next You should customize the error messages that are related to the password policy to provide the password requirements. Choose Guest Access Configure Sponsored-Guest Portals or Self-Registered Guest Portals Edit Portal Page Customization Error Messages. Search for the keyword “policy.” Rules for Guest Username Policies Cisco ISE has the following built-in rules for guest username policies:. Changes to the guest username policy do not affect existing accounts, until the guest accounts have expired and need to be changed. The special characters, /, and% cannot be used. Minimum length and minimum required characters apply to all system-generated usernames, including usernames based on email addresses. Passwords cannot match usernames.
Set the Guest Username Policy You can configure rules for how guest usernames are created. A generated username can be created based on the email address, or based on the first name and last name of the guest. The Sponsor can also create a random number of guest accounts to save time when creating multiple guests, or when guest names and email addresses are not available.
Randomly generated guest usernames consist of a mixture of alphabetic, numeric, and special characters. These settings affect all guests.
Step 1 To define the guest username policies for all Guest and Sponsor portals, choose Work Centers Guest Access Settings Guest Username Policy. Step 2 Enter the Minimum username length (in characters) for the guest usernames. Step 3 Choose one of the options under Username Criteria for Known Guests to specify the policy for creating usernames for known guests. Step 4 Choose one of the following options under Characters Allowed in Randomly-Generated Usernames to specify the policy for creating random usernames for guests:. Use all characters from each character set. To prevent the use of certain characters, choose Custom from the drop-down menu, and delete these characters from the predefined and complete sets. Step 5 Enter the minimum number of characters to use from each set.
The total number of characters from the three character sets should not exceed the number specified in Minimum username length. Step 6 Click Save. If you do not want to save any updates you made to the settings, click Reset to revert to the last saved values. What to Do Next You should customize the error messages that are related to the username policy to provide the username requirements. Choose Work Centers Guest Access Configure Sponsored-Guest Portals, Self-Registered Guest Portals, Sponsor Portals, or My Devices Portals Edit Portal Page Customization Error Messages.
Search for the keyword “policy.” SMS Providers and Services SMS services are required when you and sponsors want to send SMS notifications to guests that are using credentialed Guest portals. Whenever possible, configure and provide free SMS service providers to lower your company's expenses. Cisco ISE supports a variety of cellular service providers that provide free SMS services to their own subscribers.
You can use these providers without a service contract and without configuring their account credentials in Cisco ISE. These include ATT, Orange, Sprint, TMobile, and Verizon.
You can also add other cellular service providers that offer free SMS services or a global SMS service provider, such as a Click-A-Tell. The default global SMS service provider requires a service contract and you must configure their account credentials in Cisco ISE. If self-registering guests pick their free SMS service provider on the Self-Registration form, SMS notifications with their login credentials are sent to them free of cost. If they do not pick their SMS service provider, then the default global SMS service provider contracted by your company is used to send the SMS notifications. If you plan to allow sponsors to send SMS notifications to guests whose accounts they have created, you should customize the sponsor portal and select all the appropriate SMS service providers that can be used by these sponsors.
If you do not select any SMS service providers for the Sponsor portal, the default global SMS service provider contracted by your company will provide the SMS services. SMS providers are configured as SMS Gateways in ISE. Email from ISE is converted to SMS by the SMS gateway. The SMS gateway can be behind a proxy server. Related Tasks Related References Configure SMS Gateways to Send SMS Notifications to Guests You must set up SMS gateways in Cisco ISE to enable:. Sponsors to manually send SMS notifications to guests with their login credentials and password reset instructions.
Guests to automatically receive SMS notifications with their login credentials after they successfully register themselves. Guests to automatically receive SMS notifications with actions to take before their guest accounts expire. When entering information in the fields, you should update all text within , such as USERNAME, PASSWORD, PROVIDERID, etc., with information specific to your SMS provider's account. Before You Begin Configure a default SMTP server to use for the SMS Email Gateway option. Step 1 Choose Administration System Settings SMS Gateway. Step 2 Click Add.
Step 3 Enter an SMS Gateway Provider Name. Step 4 Select a Provider Interface Type and enter the required information:. SMS Email Gateway to send SMS via an email server. SMS HTTP API to send SMS via an HTTP API (GET or POST method). For information about configuring an SMS Email Gateway and an SMS HTTP API gateway, see. Step 5 Check Break up long message into multiple parts to enable Cisco ISE to divide messages that exceed 140 bytes into multiple messages. Most SMS providers divide long SMS messages into multiple parts automatically.
MMS messages can be longer than SMS messages. Step 6 Click Submit. What to Do Next If you configured a new SMS gateway, you can:. Select the SMS service provider to use when sending SMS notifications about expiring accounts to guests. Specify which of the configured SMS providers should display on the Self-Registration form for self-registering guests to pick from. Guest Portals When people visiting your company wish to use your company’s network to access the internet, or resources and services on your network, you can provide them network access through a Guest portal.
Employees can use these Guest portals to access your company’s network, if configured. There are three default Guest portals:. Hotspot Guest portal—Network access is granted without requiring any credentials. Usually, an Acceptance of User Policy (AUP) must be accepted before network access is granted. Sponsored-Guest portal—Network access is granted by a sponsor who creates accounts for guests, and provides the Guest with login credentials. Self-Registered Guest portal—Guests can create their own accounts credentials, and may need sponsor approval before they are granted network access.
Cisco ISE can host multiple Guest portals, including a predefined set of default portals. The default portal themes have standard Cisco branding that you can customize through the Admin portal. Wireless setup has its own default theme (CSS) and you are able to modify some basic settings such as logo, banner, background image, coloring and fonts.
In ISE, you can also choose to further customize your portal by changing more settings and go into advanced customizations. Credentials for Guest Portals Cisco ISE provides secured network access by requiring guests to log in using various types of credentials. You can require that guests log in using one or a combination of these credentials.
Username—Required. Applies to all guests using end-user portals (except Hotspot Guest portals) and is derived from the username policy.
The username policy applies only to system-generated usernames and not to usernames specified using the Guest API programming interface or the self-registering process. You can configure the policy settings that apply to usernames at Work Centers Guest Access Settings Guest Username Policy. Guests can be notified of their username in an email, SMS, or in printed form. Password—Required. Applies to all guests using end-user portals (except Hotspot Guest portals) and is derived from the password policy. You can configure the policy settings that apply to passwords at Work Centers Guest Access Settings Guest Password Policy. Guests can be notified of their password in an email, SMS, or in printed form.
Access code—Optional. Applies to guests using the Hotspot Guest and Credentialed Guest portals. An access code is primarily a locally known code that is given to physically present guests (either visually via a whiteboard or verbally by a lobby ambassador). It would not be known and used by someone outside the premises to gain access to the network.
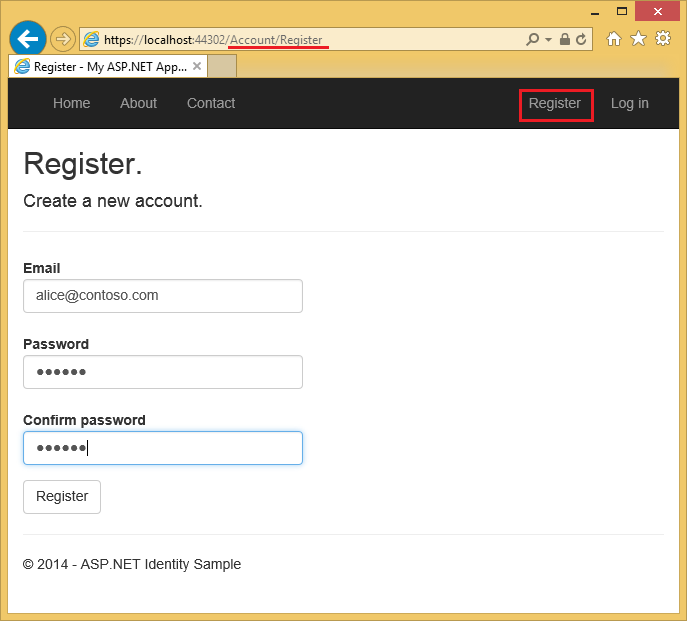
If the Access code setting is enabled:. Sponsored guests are prompted to enter it on the Login page (along with a username and password). Guests using the Hotspot Guest portal are prompted to enter it on the Acceptable Use Policy (AUP) page. Registration code—Optional.
Applies to self-registering guests and is similar to an access code in how it is provided to the self-registering guests. If the Registration code setting is enabled, self-registering guests are prompted to enter it on the Self-Registration form. The username and password can be provided by a sponsor at your company (for sponsored guests), or a Credentialed Guest portal can be configured to allow guests to register themselves to obtain these credentials. Related Concepts Related References Guest Access with Hotspot Guest Portals Cisco ISE provides network access functionality that includes “hotspots,” which are access points that guests can use to access the Internet without requiring credentials to log in. When guests connect to the hotspot network with a computer or any device with a web browser and attempt to connect to a website, they are automatically redirected to a Hotspot Guest portal. Both wired and wireless (Wi-Fi) connections are supported with this functionality.
The Hotspot Guest portal is an alternative Guest portal that allows you to provide network access without requiring guests to have usernames and passwords and alleviates the need to manage guest accounts. Instead, Cisco ISE works together with the network access device (NAD) and Device Registration Web Authentication (Device Registration WebAuth) to grant network access directly to the guest devices. Sometimes, guests may be required to log in with an access code. Typically, this is a code that is locally provided to guests who are physically present on a company’s premises. If you support the Hotspot Guest portal:.
Based on the Hotspot Guest portal configuration and settings, guests are granted access to the network if the guest access conditions are met. Cisco ISE provides you with a default guest identity group, GuestEndpoints, which enables you to cohesively track guest devices. Guest Access with Credentialed Guest Portals You can use a credentialed Guest portal to identify and authorize temporary access for external users to internal networks and services, as well as to the Internet. Sponsors can create temporary usernames and passwords for authorized visitors who can access the network by entering these credentials in the portal's Login page.
You can set up a credentialed Guest portal so that guests can log in using a username and password that is obtained:. From a sponsor. In this guest flow, guests are greeted by a sponsor, such as a lobby ambassador, when they enter company premises and are set up with individual guest accounts.
After they register themselves, using an optional registration code or access code. In this guest flow, guests are able to access the Internet without any human interaction and Cisco ISE ensures that these guests have unique identifiers that can be used for compliance.
After they register themselves, using an optional registration code or access code, but only after the request for a guest account is approved by a sponsor. In this guest flow, guests are provided access to the network, but only after an additional level of screening is done. You can also force the user to enter a new password when logging in. Cisco ISE enables you to create multiple credentialed Guest portals, which you can use to allow guest access based on different criteria. For example, you might have a portal for monthly contractors that is separate from the portal used for daily visitors. Employee Access with Credentialed Guest Portals Employees can also access the network using Credentialed Guest Portals by signing in using their employee credentials, as long as their credentials can be accessed by the identity source sequence configured for that portal. Guest Device Compliance When guests and non-guests access the network through credentialed Guest portals, you can check their devices for compliance before they are allowed to gain access.
You can route them to a Client Provisioning page and require them to first download the posture agent that checks their posture profile and verifies if their device is compliant. You can do this by enabling the option in the Guest Device Compliance Settings in a credentialed Guest portal, which displays the Client Provisioning page as part of the guest flow. The Client Provisioning service provides posture assessments and remediations for guests. The Client Provisioning portal is available only with a Central Web Authorization (CWA) guest deployment. The guest login flow performs a CWA, and the credentialed Guest portal is redirected to the Client Provisioning portal after performing acceptable-use-policy and change-password checks.
The posture subsystem performs a Change of Authorization (CoA) on the network access device to reauthenticate the client connection once the posture has been assessed. Guest Portals Configuration Tasks You can use a default portal and its default settings such as certificates, endpoint identity group, identity source sequence, portal themes, images, and other details provided by Cisco ISE. If you do not want to use the default settings, you should create a new portal or edit an existing one to meet your needs. You can duplicate a portal if you want to create multiple portals with the same settings. After creating a new portal or editing a default one, you must authorize the portal for use.
Once you authorize a portal for use, any subsequent configuration changes you make are effective immediately. If you choose to delete a portal, you must first delete any authorization policy rules and authorization profiles associated with it or modify them to use another portal.
Use this table for the tasks related to configuring the different Guest portals.